Free SNI Bug Hosts for South Africa (Vodacom, MTN, Telkom, Cell C) – Full Beginner Guide
If you're familiar with VPN tunneling apps such as HA Tunnel Plus, HTTP Custom, V2Ray, or TLS Tunnel, then you've probably seen people talking about SNI bug hosts especially in South Africa. These hosts are often associated with free internet tricks, configuration files, and network bypassing. While many of the online discussions can be confusing, the concept of SNI is actually quite simple once broken down.
This guide explains what SNI bug hosts really are, how they are used on different South African networks (Vodacom, MTN, Telkom, and Cell C), and why they matter for anyone learning about tunneling, networking, or cybersecurity.
What Are SNI Bug Hosts?
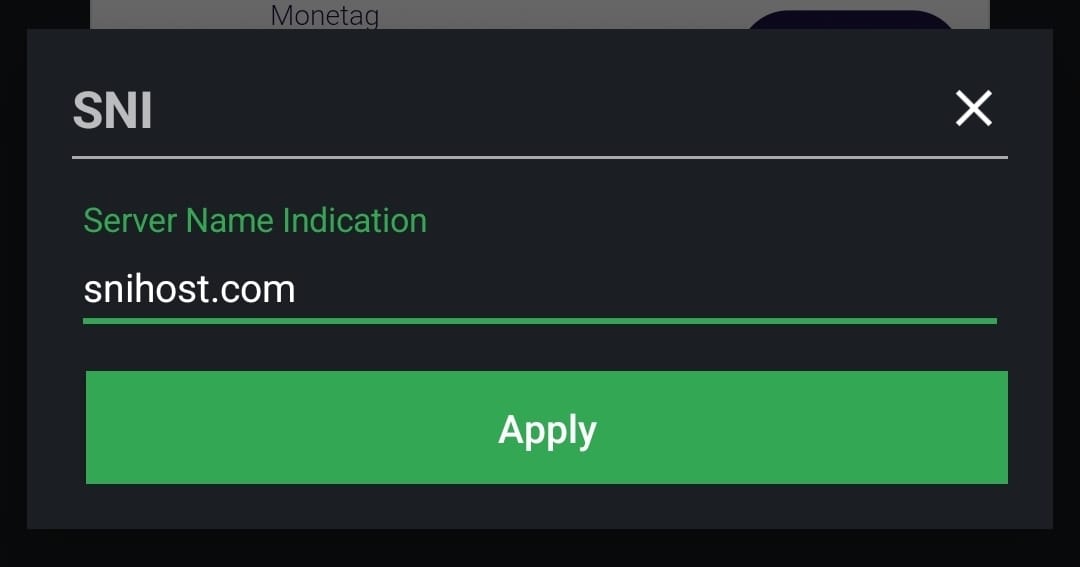
SNI stands for Server Name Indication, a TLS/SSL feature that tells a server which website you are trying to reach. Mobile networks use SNI to manage and route traffic, including special websites that they allow even when a user has no active data bundle. These are known as zero-rated websites.
A "bug host" is simply an SNI domain that responds differently than expected—usually because it is part of a free-access website, promo site, or customer portal. When these hosts are used inside VPN tunneling apps, they can sometimes establish a connection even when regular data is unavailable.
In simple terms:
An SNI bug host is a domain that a network allows to load for free, and VPN apps use this to create a connection.
Are SNI Bug Hosts Legal?
It's important to clarify this:
Legal
Learning how SNI works
Not Allowed
Using a domain to intentionally bypass billing systems
Important Notice
This blog will not provide any real bug hosts, exploits, or bypass tricks. Instead, we focus on safe, educational explanations—helpful for networking students, VPN creators, and cybersecurity beginners.
Why SNI Bug Hosts Are Popular in South Africa
South Africa has four main networks:
Vodacom
MTN
Telkom
Cell C
All of them offer various zero-rated services such as:
- Educational portals
- COVID-19 public information sites
- Government websites
- Self-service apps
- Social media free-modes
These are the domains that often become "SNI hosts" because the network allows them without active data.
Many users online test these domains inside VPN apps to see if they allow a handshake or tunnel connection. Sometimes they work, sometimes they don't, and sometimes they stop working quickly.
How SNI Bug Hosts Work on SA Networks
1Vodacom
Vodacom uses strict routing but has zero-rated pages for:
- • Social media portals
- • Self-service login pages
- • Public services
Because they use deep filtering, SNI success varies widely.
2MTN
MTN is known for educational zero-rated websites and special promo portals.
Many users experiment with these domains, but MTN regularly updates their firewall rules.
3Telkom
Telkom historically had more open routing, which is why tunneling apps gained popularity among users.
Today, Telkom is more secure but still supports many free-access services.
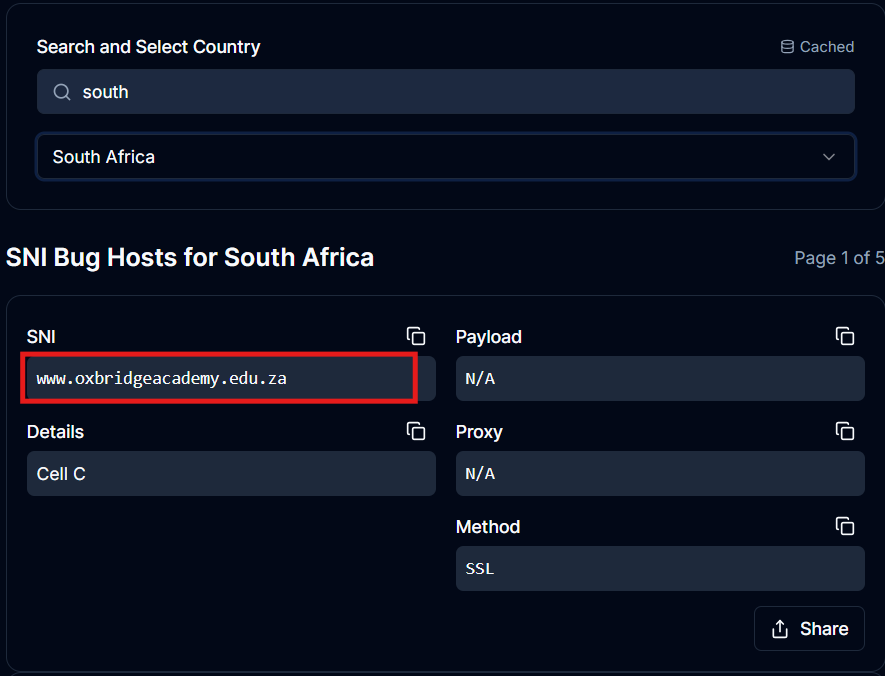
4Cell C
Cell C works with similar zero-rated programs and promotional portals.
Its flexibility is one reason why many online groups focus on Cell C SNI testing.

Where Do People Usually Get SNI Bug Hosts?
Since real working bug hosts cannot be publicly posted safely or legally, users usually rely on:
Official zero-rated service lists
All SA networks publish lists of websites that are free to access. These are safe and legitimate.
Host generator tools
Platforms like SNI generators help people discover valid domains, not exploits.
Get SNI Hosts HereCommunity forums (safe discussions only)
Users often share research insights, not illegal bypass files.
Network analysis for learning purposes
Students sometimes test how SNI behaves to understand TLS handshakes or firewall behavior.
What You Should NOT Do With SNI Hosts
To stay safe and compliant with network terms, avoid:
- Using SNI hosts to bypass data billing
- Sharing real bug hosts online
- Downloading risky "free internet" files from unknown sources
- Using tunneling apps to exploit network systems
These can lead to:
❌ Account suspensions
❌ SIM blocking
❌ Security risks
❌ Malware from fake config files
Always prioritize safe learning.
How to Use SNI Hosts for Legitimate Purposes
Even without bypassing networks, SNI hosts are valuable for:
Cybersecurity learning
Understanding how TLS works is essential for ethical hacking and penetration testing.
VPN configuration testing
Developers test SNI behavior to create secure connection methods.
Website deployment
Admins must ensure their domains handle SNI correctly to avoid security issues.
Research on digital access
Zero-rated services are often studied by students and digital policy researchers.
🎯 Final Thoughts
SNI bug hosts are widely discussed in South Africa because networks offer zero-rated sites that sometimes behave differently in tunneling scenarios. While you should never use SNI hosts to bypass billing systems, learning how they work is extremely valuable for anyone interested in:
Networking
VPN Development
Cybersecurity
Internet Access Research
If you want to safely explore domains, always stick to public, official zero-rated sites or a domain generator tool that gives educational insights—not exploits.