How to Decrypt HA Tunnel Plus Files (HAT Files) in 2025
🔍 Introduction
Locked HA Tunnel Plus configuration files (HAT files) hide the SNI host, payload, and tunneling tweaks that keep free-internet methods alive. This 2025 playbook walks you through decrypting any file in minutes using the official HA Tunnel Decrypt Bot on Telegram.
Why Decrypt?
- Extract SNIs and payloads from proven configs
- Reverse-engineer what expert config makers do
- Fix files that suddenly stopped connecting
Quick Stats
5
Simple Steps
1s
Avg decrypt
0
Coding Needed
100%
Success rate
🔐 Why Decrypt HA Tunnel Files?
Decrypting HAT files lets you peek under the hood of premium, invite-only configs so you can recreate them for your own SIM or region. You’ll see the exact combination of SNI, payload, SSH host, and tunneling method that makes them work.
Common motivations:
- Extract SNI bug hosts that still bypass throttling
- Copy payload headers into TLS Tunnel, HTTP Custom, or DroidVPN
- Learn how advanced config creators layer SSH accounts
- Troubleshoot a file that stopped working overnight
Data you’ll reveal
SNI bug host and fallback domain
Payload script + HTTP headers
SSH credentials (if embedded)
Connection type, proxy, and metadata
🧰 Requirements
Gather these before you start:
Phone or PC
Android, iOS, Windows, or macOS works.
Locked HAT File
The configuration you want to inspect.
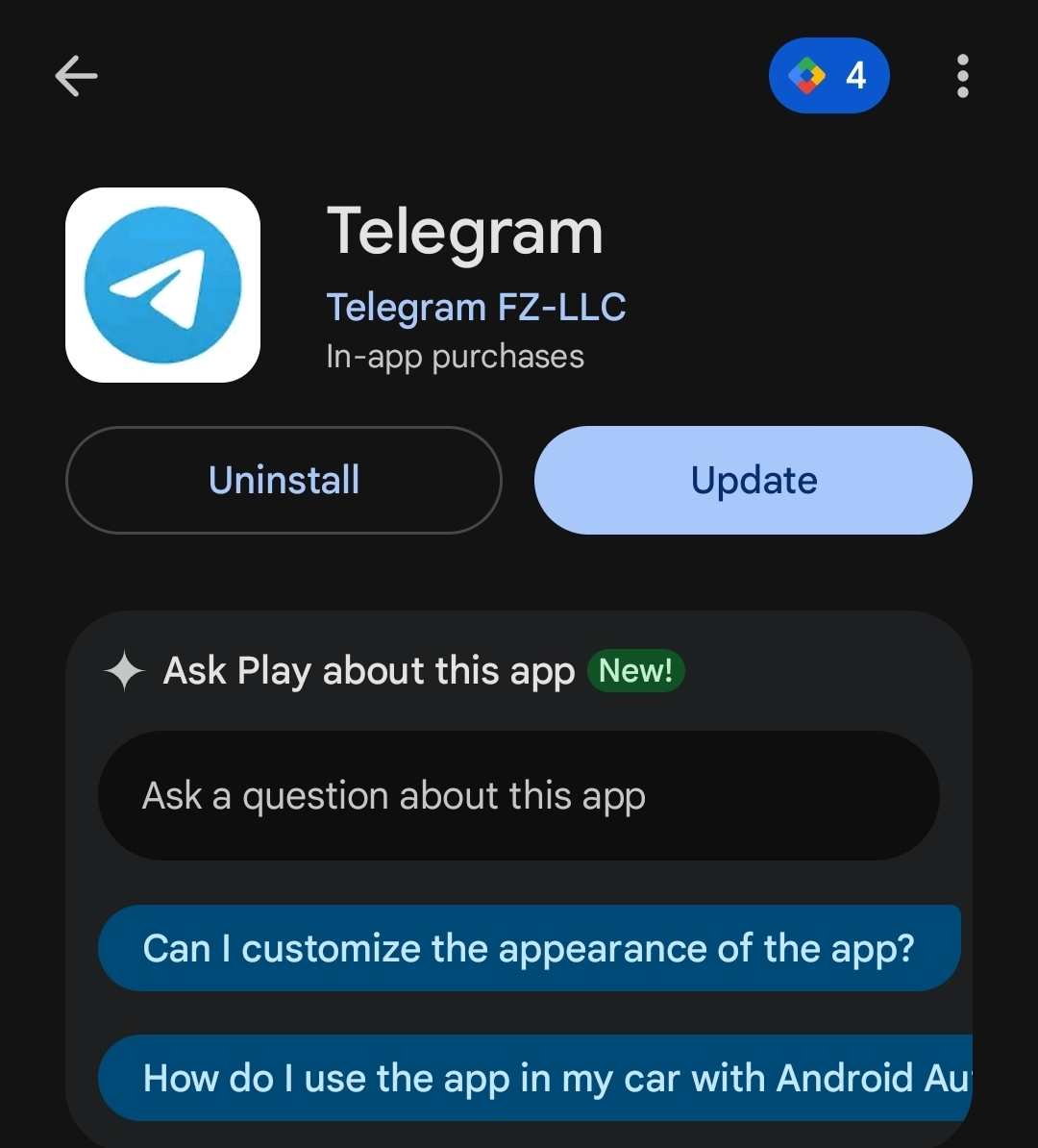
Image 1: Telegram search area ready for the bot.
Install or Open Telegram
Mobile and desktop both work.
Log in to Telegram on the same device that holds your HAT file. Telegram Web is perfect if you stored the file on a laptop.
Available on Android, iOS, Windows, and macOS.
Find the HA Tunnel Decrypt Bot
The official bot unlocks any HAT file.
You can locate the bot manually or open it instantly:
1Method 1: Search inside Telegram
- Tap the global search bar.
- Enter
HA Tunnel Decrypt Bot. - Pick the bot with the correct icon.
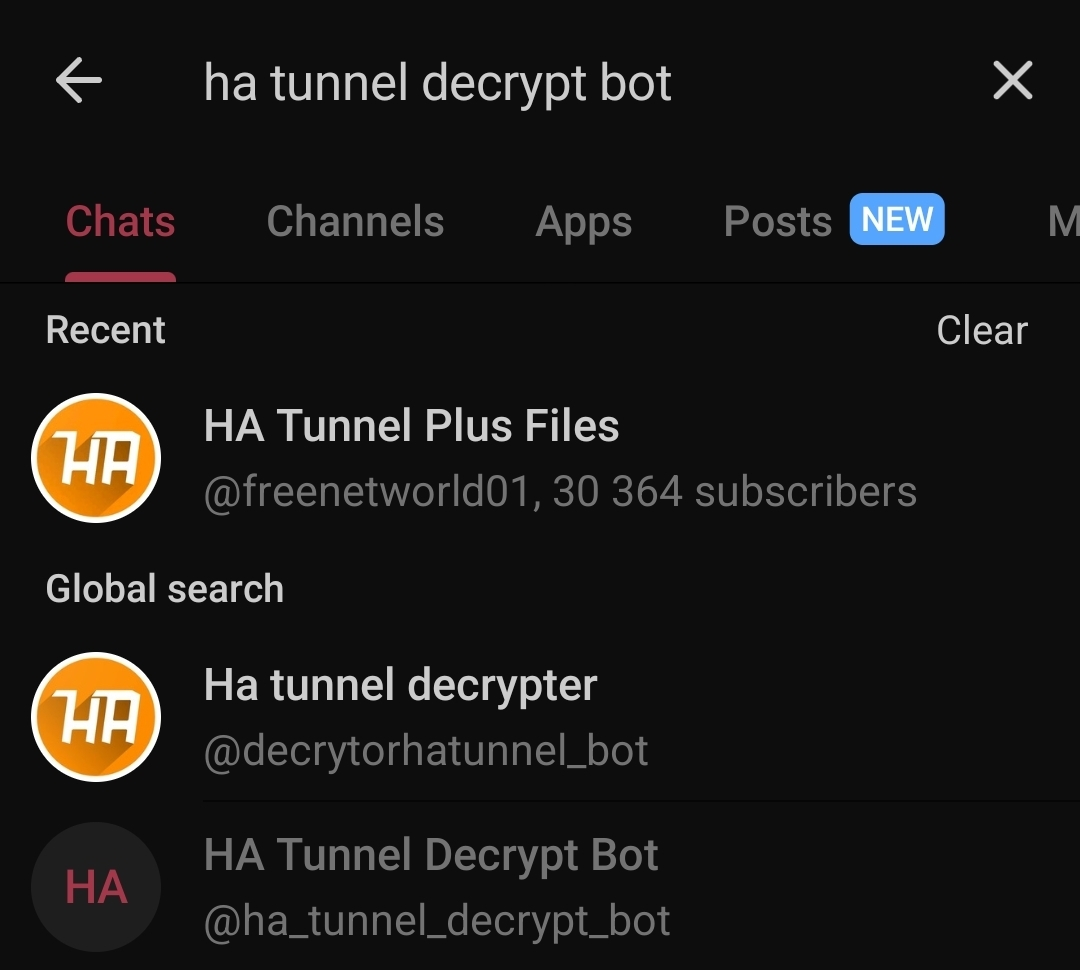
Telegram search results

Image 3: Bot welcome screen with the Start button.
Start the Bot
It guides you automatically.
Inside the chat:
- Tap Start to activate the bot.
- Wait for the welcome message and instructions.
- The bot tells you to upload your locked HAT file.
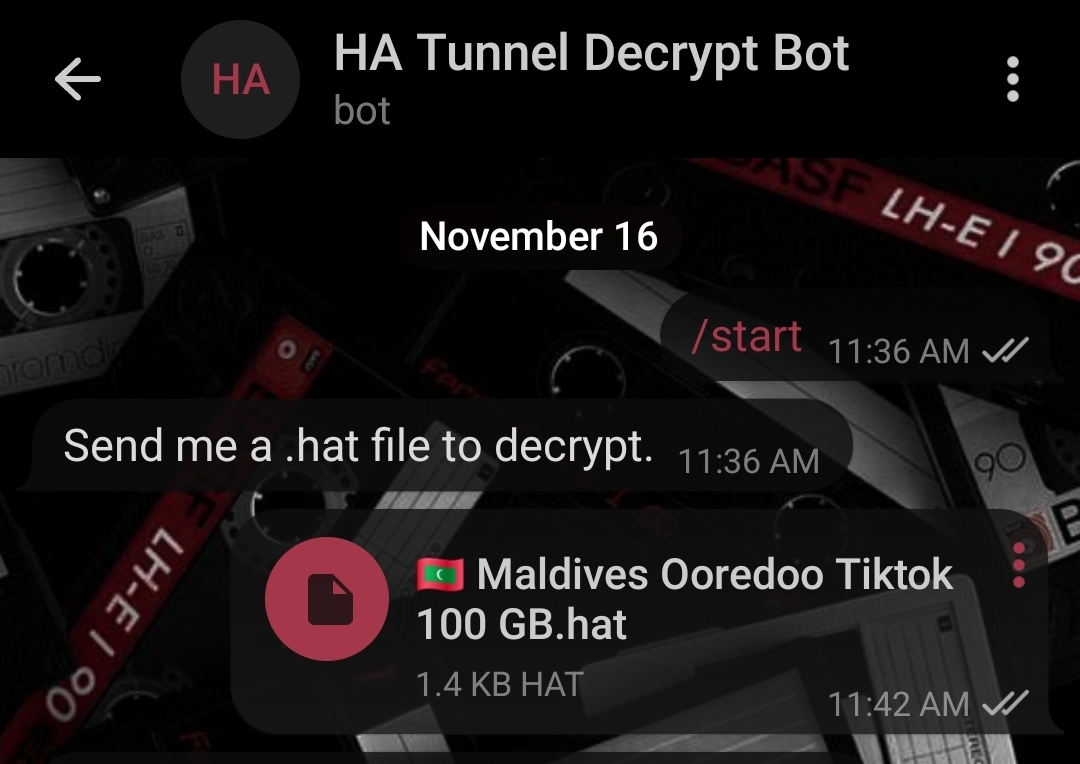
Image 4: Uploading the locked file.
Upload Your Locked HAT File
Drag-and-drop works great.
Send the configuration directly to the bot:
- Tap the attachment icon.
- Select the locked HAT file from your storage.
- Send it and wait a second while the bot processes it.
Decryption normally finishes in under one second.

Image 5: Example of decrypted output.
Read the Decrypted Output
Everything is now human-readable.
The bot instantly replies with a clean text version of the file. Expect to see:
Copy the values you need, rebuild the config inside HA Tunnel Plus, and save a backup so you never lose the recipe.
🎯 After You Decrypt a HAT File
Study the Structure
See exactly how the creator combined payloads, SNI, and SSH.
Extract Working SNIs
Reuse bug hosts that match your carrier or APN.
Troubleshoot Issues
Compare a broken file with a working one and spot the difference.
Create Better Backups
Store decrypted notes so you can rebuild with new SSH accounts anytime.
🛡️ Safety Notes
The HA Tunnel Decrypt Bot is safe because it simply reads the file, converts it to text, and sends the result back to you. It never asks for personal logins.
- No additional software required.
- All communication stays inside Telegram.
- You can delete conversations afterward.
🎯 Final Thoughts
You now have the same workflow top config makers use to unlock HA Tunnel files in seconds. Use these decrypted insights to craft your own zero-rated builds, fix broken tunnels, or teach your community how the magic works.
Last updated: November 16, 2025 • v1.3.0